Define
We define a scope of work with industry to solve a pressing cybersecurity challenge.

We invite members of the community to talk about their challenges, ask questions, and listen to understand the challenge at hand. During this phase, we publish a draft project description for public comment. We adjudicate the comments and publish a final version to our website that outlines the cybersecurity challenge along with a draft architecture.
Assemble
We assemble teams of industry organizations, government agencies, and academic institutions to address all aspects of a cybersecurity challenge.

We release a Federal Register Notice to announce the opportunity to collaborate and explain what capabilities we are looking for. Potential collaborators respond with a completed Letter of Interest (LOI). Submitted LOIs are accepted on a first-come basis. When the collaborators join our build team, they sign a Cooperative Research and Development Agreement (CRADA) to provide their commercially-available product and their expertise. All our work is open, transparent, publicly accessible, and informed by both the general public and technology providers.
Build
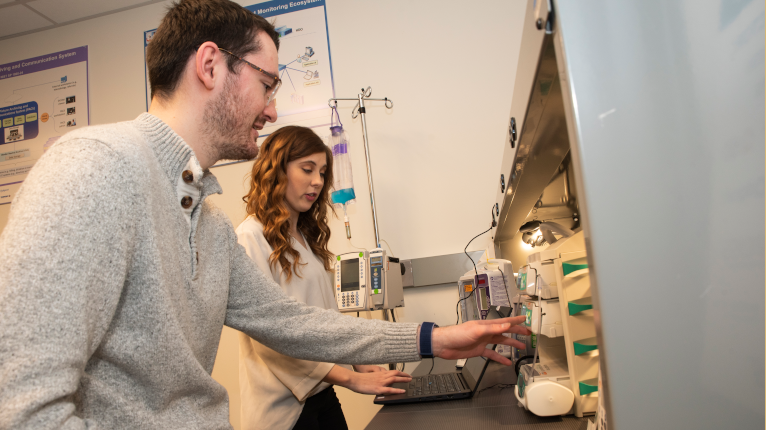
We build a practical, usable, repeatable implementation to address the cybersecurity challenge. During this phase, a reference architecture is finalized. The collaborators provide support to install and configure their technologies and then they provide support throughout the build to address issues, such as interoperability.
